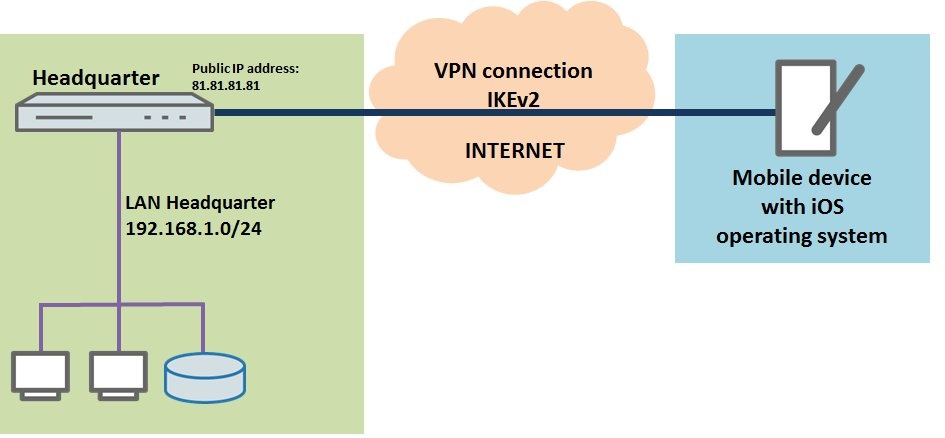
Description:This document describes how you set up a
network connection using an IKEv2 client-to-site VPN connection between a smartphone or tablet PC equipped with the iOS operating system and a LANCOM router.
Requirements:- Mobile device (smartphone, tablet PC, etc.) with the iOS version 9.x
Scenario:- A company wants its sales representatives to have access to the corporate network via IKEv2 client-to-site connection.
- Employees should be able to use their mobile iOS devices (smartphone, tablet PC, etc.) to connect via VPN.
- The company headquarters has a LANCOM router as a gateway with an Internet connection with the fixed public IP address 81.81.81.81.
- The local network at the headquarters has the IP address range 192.168.1.0/24.
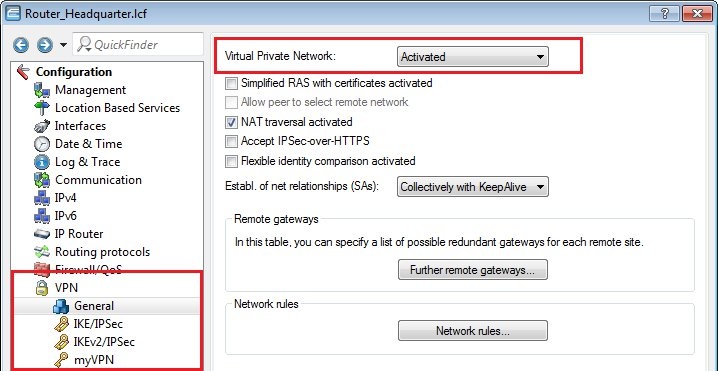
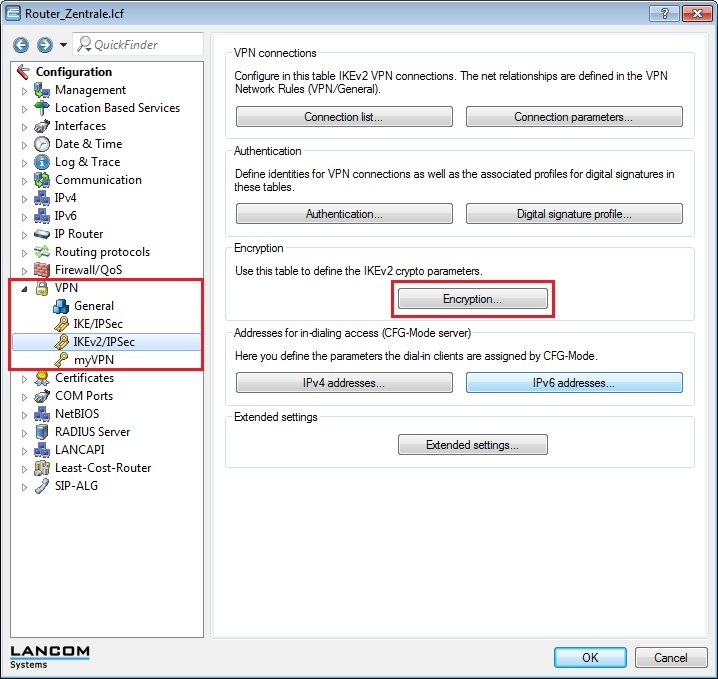
Procedure:1) Manual configuration of the LANCOM router at the headquarters:1.1) Open the configuration for the LANCOM router at the headquarters and switch to the menu item
VPN -> General.
1.2)
Enable the function
Virtual Private Network.
1.3) Open the menu item
VPN -> IKEv2/IPSec and click the button
Authentication.
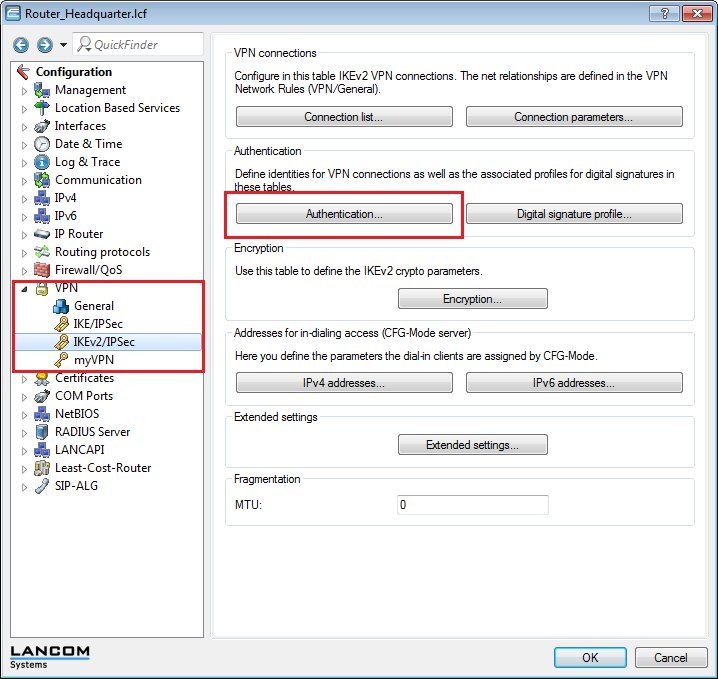
1.4) Click on the
Add... button to create a new entry.
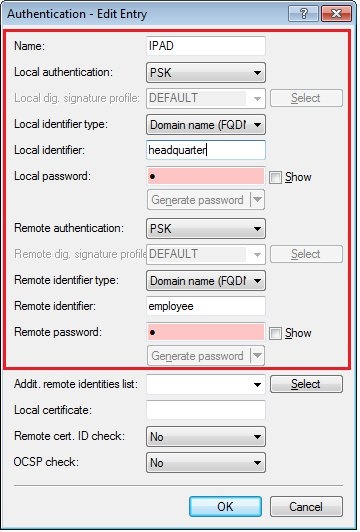
1.5) Enter the
information for the authentication of the VPN connection into the configuration window.
Name:Enter the
name for the authentication here. This entry is used later in the VPN connection list (see step 1.8).
Local authentication:Select the
authentication type used on the router at the headquarters. This example uses authentication by
pre-shared key (PSK).
Local identifier type:Set the
identifier type for the router at the headquarters to the parameter
Domain name (FQDN).
Local identifier:Set the local identifier. In this example, the
LANCOM router at the headquarters uses the
local identity "headquarter".
Local password:Set the
pre-shared key to be used to authenticate at the router at the headquarters.
Remote authentication:Select the
authentication type used by the remote iOS device. This example uses authentication by
pre-shared key (PSK).
Remote identifier type:Set the
identifier type for the iOS device to the parameter
Domain name (FQDN).
Remote identifier:Set the remote identifier. In this example, the iOS device uses the
remote identifier "employee".
Remote password:Set the
pre-shared key to be used to authenticate at the iOS device.
Enter the same password that you used as local password.Remote cert. ID check:As this function is not required, set this to
no..
1.6) Open the menu item
VPN -> IKEv2/IPSec and click the button
Encryption.
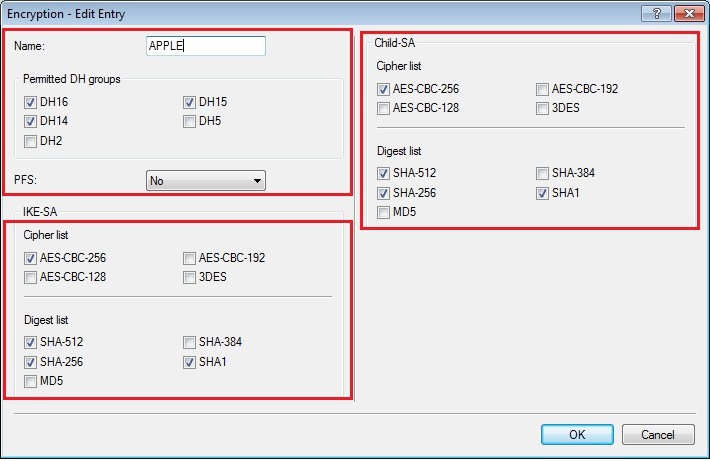
1.7) Click on the
Add... button to create a new entry.
- Enter a name for the new encryption profile.
- Configure the parameters as shown in the following figure. It is important that the parameter PFS is disabled.
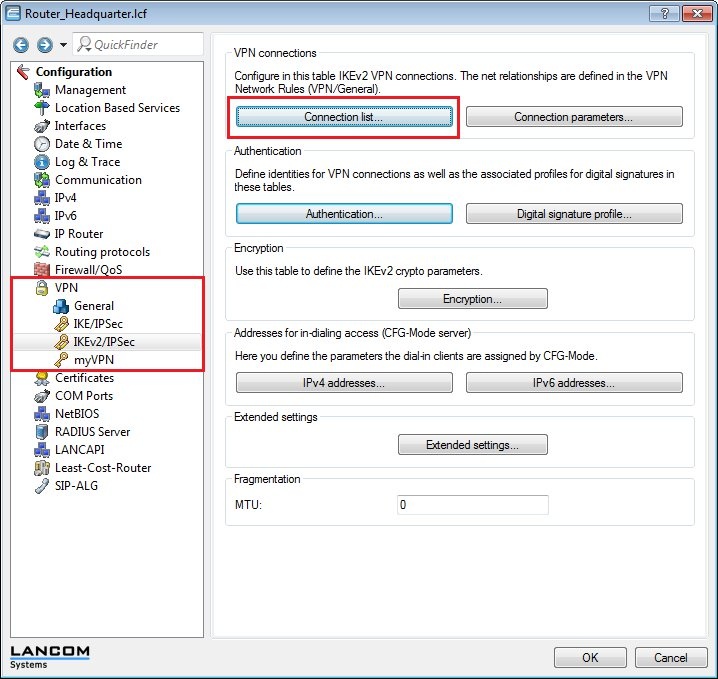
1.8) Open the menu item
VPN -> IKEv2/IPSec and click the button
Connection list.
1.9) Click on the
Add... button to create a new entry.
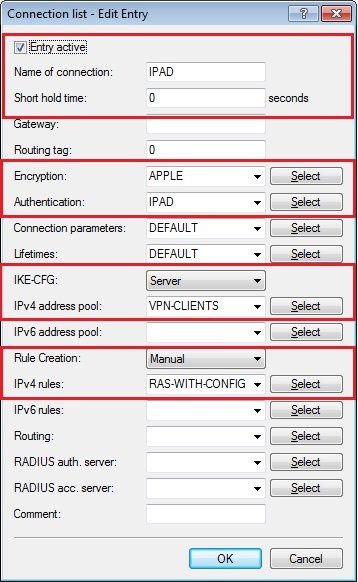
1.10) Enter the following information into the configuration dialog:
Connection name:Enter a name for the VPN connection.
Short hold time:Specify the short-hold time in seconds for the VPN connection. In this example, a 0 is entered into the LANCOM router at the headquarters. This means that this router will not actively establish the VPN connection.
Eonryption:Select the encryption profile that you created in step 1.7.
Authentication:Select the authentication. The entry here corresponds to the name of the authentication that you set in step 1.5.
IKE-CFG:This parameter is set to
Server.
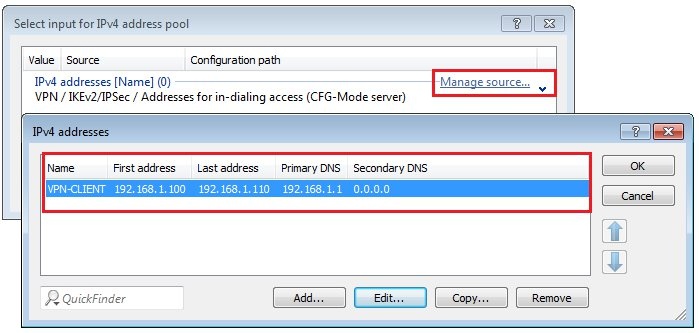
IPv4 address pool:Here you set a
local IP addresses range, from which each dial-in VPN client is assigned an IP address. If you have not specified an address pool yet, click on the
Select button and, in the dialog that follows, click the link
Manage source...Info:In IKEv2 connections an IPv4 address pool must be a configured in this dialog. The use of address pools in the dialogues
Communication -> Remote sites -> WAN tag tableIPv4 -> addresses has no effect on IKEv2 connections, they are only used for IKEv1 connections.
Create an IPv4 address pool in the following dialog.
 Rule creation:Rule creation must be performed manually
Rule creation:Rule creation must be performed manually.
IPv4 rules:Here you set the parameter
RAS-WITH-CONFIG-PAYLOAD.
1.11) Write the configuration back to the LANCOM router at the headquarters.
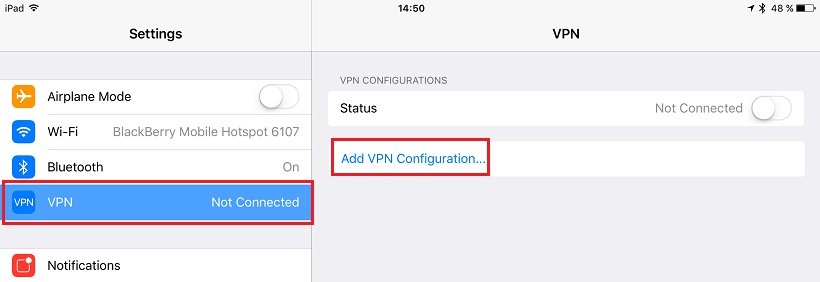
2) Manual setup of the VPN connection on your smartphone or tablet PC:2.1) Open the system
Settings your iOS device and tap the option
VPN.
2.2) Then tap on the option
Add VPN configuration.
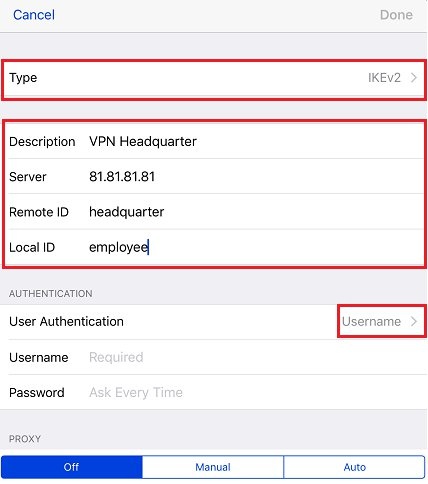
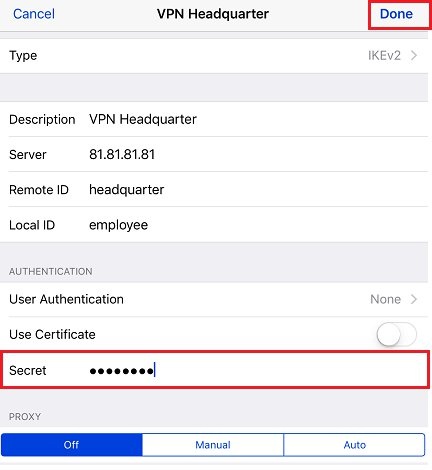
2.3) Set the connection type to
IKEv2.
- Insert a description of your choice into the Description field.
- In the Server field, enter the public IP address or public DNS name of the LANCOM router at the headquarters. In this example it is 81.81.81.81.
- Set the Remote ID to the value that you configured in step 1.5 as the local identity for the headquarters.
- Set the Local ID to the value that you configured in step 1.5 as the remote identity for the iOS device.
2.4) Then tap on the option
Username.
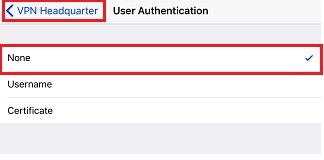
2.5) Select the value for
User authentication as
None.
Then use the link in the upper left corner to return to the VPN connection profile.
2.6) In the
Shared secret field, enter the
pre-shared key that you set when
configuring the LANCOM router in step 1.5.
2.7) Select
Done to complete the configuration of the VPN connection profile.
2.8) Tap on the
entry for the VPN connection profile and the VPN connection is established to the LANCOM router at the headquarters.
