Description:
As of LCOS version 10.30 you can create application-specific rules in the firewall of a LANCOM router with which Internet applications (e.g. Office 365, Salesforce, etc.) can be routed to a particular default route.
By means of layer-7 application control, you can keep control over how applications communicate on your network.
This document describes how, in a scenario where a VPN connection is a default route, you can use DNS names to break-out particular types of data traffic to the Internet.
Requirements:
- LANtools version 10.30 or later (download)
- LCOS version 10.30 or later (download)
The LANCOM router must operate as a DNS server or DNS forwarder in the network. Clients on the local network must
use the router as a DNS server. In addition, clients need to be prevented from using DNS-over-TLS and DNS-over-HTTPS (also in
the browser) directly with external DNS servers.
This can be achieved with the following options:
- The DHCP server has to communicate the IP address of the router as a DNS server. The Internet Setup Wizard configures this by default.
- Firewall rules have to be set up to prevent the direct use of external DNS servers, e.g. by blocking the outgoing UDP port 53 for clients on the source network.
- Firewall rules have to be set up that prevent the direct use of external DNS servers that support DNS-over-TLS, e.g. by blocking the outgoing TCP port 853 for clients on the source network.
- Disable DNS-over-HTTPS (DoH) in the browser.
Notes on how to synchronize the firewall's DNS database:
Since the firewall learns its information from the DNS requests of the clients, in certain situations the DNS database will be incomplete. This can happen in the following situations:
- A new firewall rule is added, but the client still has a cached DNS entry.
- The router was restarted when the client already has a cached DNS entry.
Helpful in these cases is emptying the DNS cache on the client, rebooting the client, or a time-out of the
DNS record on the client.
The router’s own services, such as ping, are not handled by the firewall rules. By sending a ping to a full DNS name (without wildcard expressions), the generation of rule resolutions (DNS to IP addresses) can be performed on-demand either from the command line (once) or by a cron job.
Note:
Different DNS names that resolve to the same IP address cannot be distinguished. In this case, the first rule that references one of these DNS names will apply. That should not be a problem for large service providers. However, it could occur with small websites hosted by the same vendor.
Example scenario:
Layer-7 application control allows the communication to various web services (such as cloud services like Salesforce) to break-out locally. This prevents this data traffic from first being routed via the VPN connection to the main office and breaking-out there.
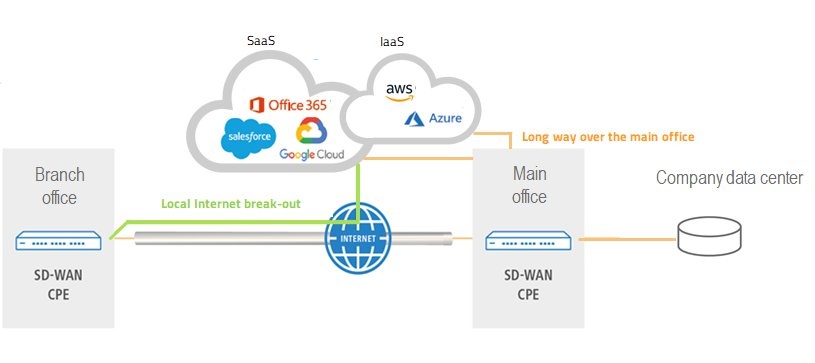
- In this example configuration, an Internet connection at the branch office is established via a VPN connection to the main office. Any traffic destined for the Internet will be routed to the main office via the VPN connection.
- The branch office has two default routes:
- The MAIN-OFFICE VPN with routing tag 0 for communication to the main office via the VPN connection, and
- INTERNET with routing tag 1 for establishing the Internet connection
- The traffic to the CRM provider Salesforce should break-out via the local Internet connection.
Procedure:
The Internet connection and the VPN connection used in this example are already functional.
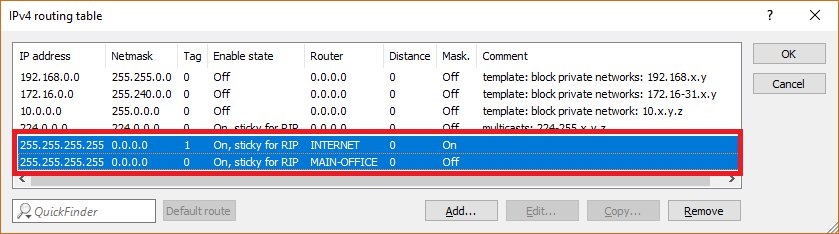
- The connection MAIN-OFFICE VPN in the IPv4 routing table is set as a default route with the routing tag 0.
- The connection INTERNET is set as a default route with the routing tag 1.
Configuring a firewall rule to route traffic to the CRM vendor Salesforce via the local Internet connection:
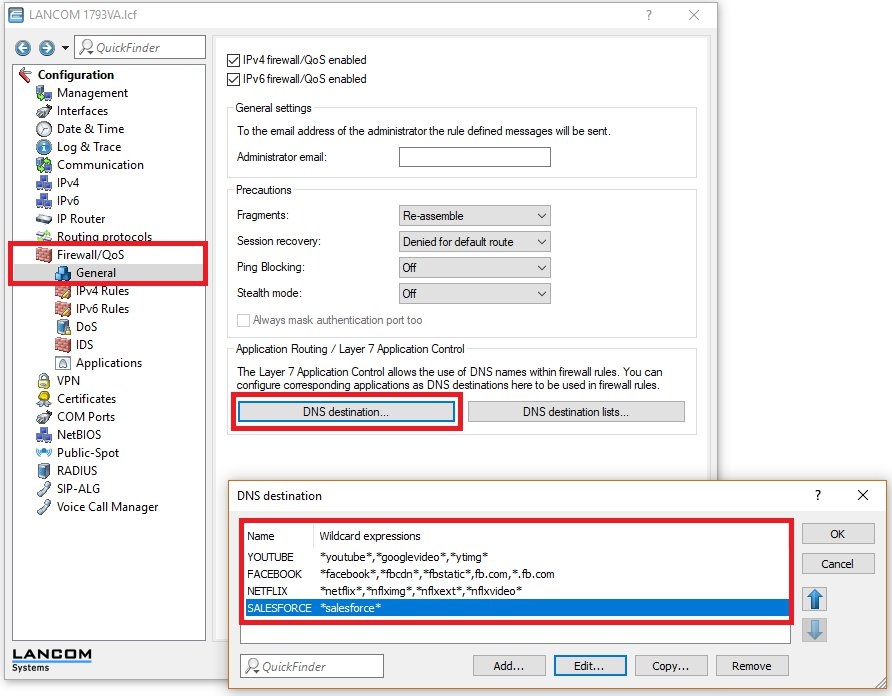
1) In order to reference DNS destinations in firewall rules, the destinations first have to be configured in the menu Firewall/QoS -> General -> DNS destination.
By default the list of DNS destinations already contains entries for the services Facebook, Youtube, Netflix and Salesforce. Further information about the DNS destination lists is available in the LCOS Reference Manual.
2) Navigate to the menu Firewall/QoS -> IPv4 rules -> Rules... and add a new firewall rule.
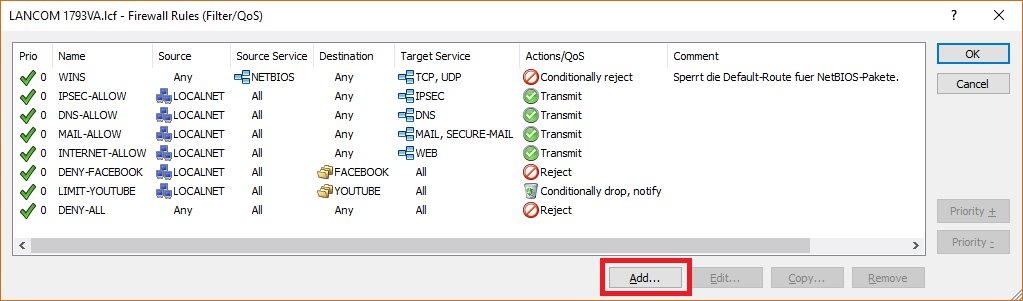
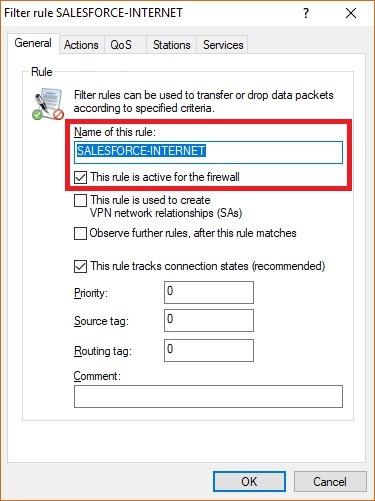
3) Give the new rule a meaningful name.
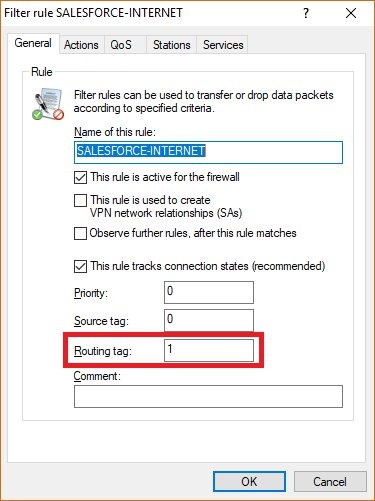
4) Set the item Routing tag to the value 1 so that this traffic is routed via the default route with the routing tag 1 (i.e. remote site INTERNET).
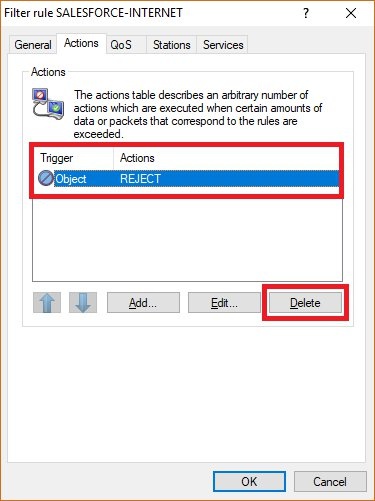
5) Now go to the Actions tab and delete the REJECT object.
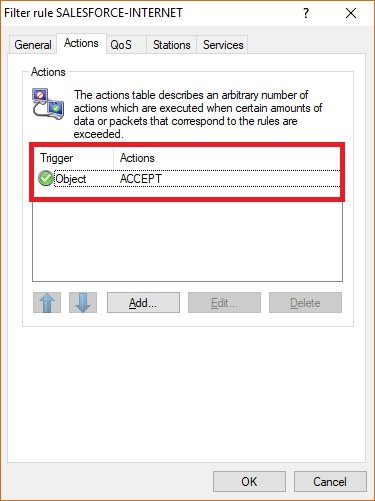
6) Click Add to add the ACCEPT object.
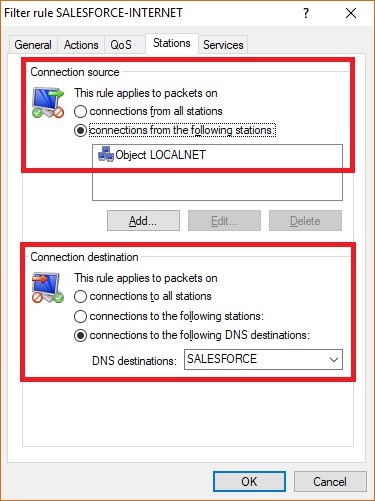
7) Go to the Stations tab. Under Connection source add the object LOCALNET, and under Connection destination add the DNS destination SALESFORCE.
8) Finally, save the firewall rule by clicking OK and write the configuration back to the router.
Note:
For
application-based routing, there is the new parameter FW-DNS for the trace command. It can monitor
changes to the firewall database of DNS destinations :
· If a DNS packet arrives, it outputs the packet along with the affected wildcard expressions and destinations.
· If the TTL (time-to-live) of an entry expires, it outputs the associated record along with the relevant wildcard expressions and destinations.
· If one of the two firewalls registers or de-registers a DNS destination because its configuration has changed.
· If there is a change to the tables
Setup -> Firewall -> DNS-Destinations or
Setup -> Firewall -> DNS-Destination-List .
|
|